


Most of my work is offensive security assessments for enterprise clients. Web apps, mobile apps, external networks, cloud environments, source code. The part that matters most to me is making sure the findings actually change something, whether that means sitting with a dev team or presenting to a CISO.

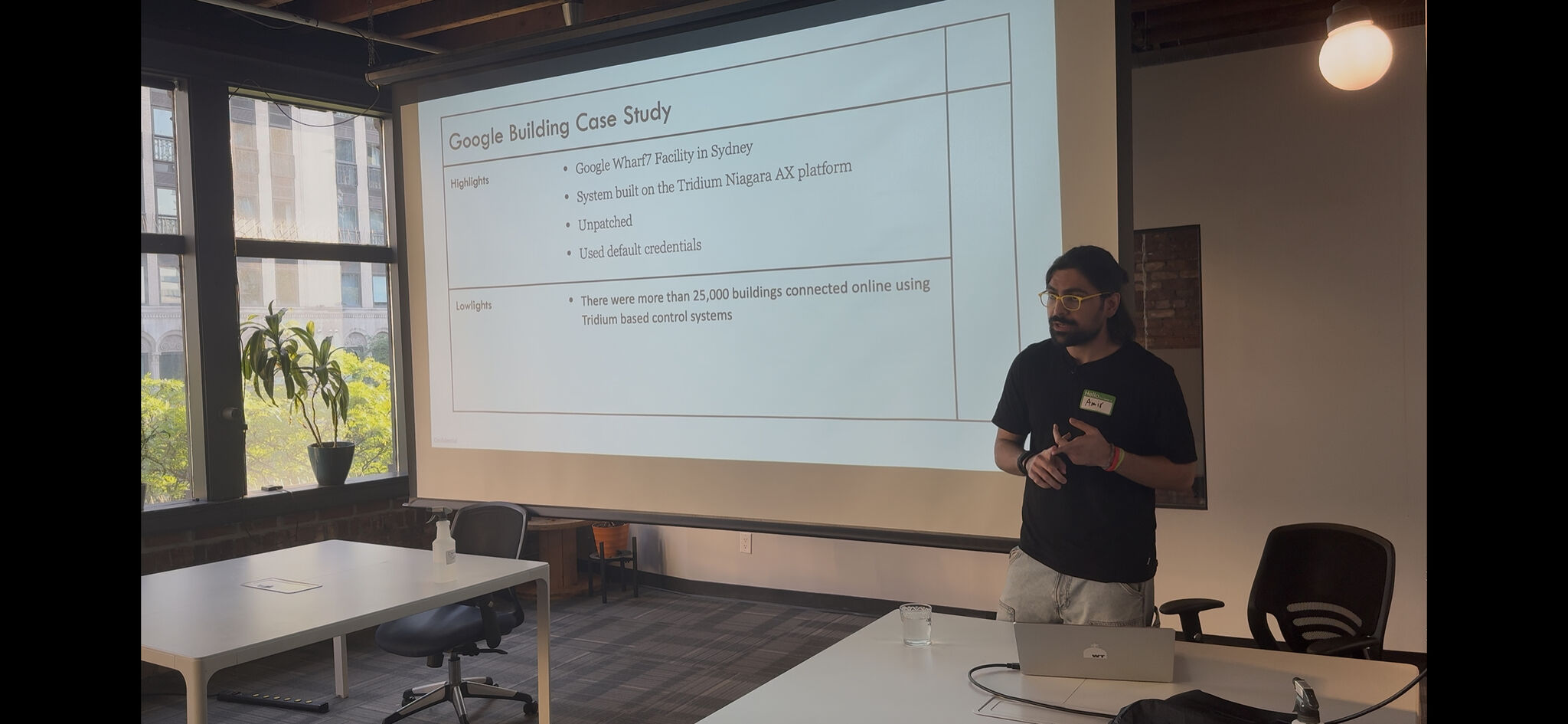


Offensive security consulting for enterprise clients, mostly in financial services and SaaS. Web application assessments, mobile app testing on iOS and Android, external network pentests, cloud security reviews, and source code audits. I handle the full engagement from scoping through the final readout.
On the side, I do bug bounty research on HackerOne. 120+ validated vulnerabilities on companies like PayPal, Sony, AT&T, Airbnb, and Booking.com. Most of my best finds are multi-step attack chains on web and mobile targets.
The thing I care about most in consulting is the report. Not because I love writing, but because a finding that doesn't change anything was a waste of everyone's time. I write differently for a developer than I do for a CISO, and I've gotten good at making both of them act on the same issue.
Before testing starts I want to know what the client actually cares about protecting. Threat model the business, not just the app. Use real threat intel to figure out who would target this client and how.
Scanners find the easy stuff. Source code review, manual testing, and understanding how the app actually works is where the real findings come from. Business logic, auth design, trust boundaries.
A report that sits in a drawer is useless. Frame findings so the dev team knows what to fix and the executive knows why to fund it. Follow up. Make sure something actually changed.
Testing: Web apps, mobile (iOS/Android), APIs, external networks, cloud (AWS, Azure, GCP), source code
Tools: Burp Suite Pro, Frida, MobSF, Objection, Nuclei, Metasploit, Cobalt Strike, Bloodhound, Nmap
Languages: Python, Go, JavaScript, Java, Swift, Bash, C, C++, Rust
Frameworks: OWASP Top 10, OWASP MASVS, MITRE ATT&CK, NIST, PTES, CVSS
If you need a security consultant who can test it and explain it, let's connect.